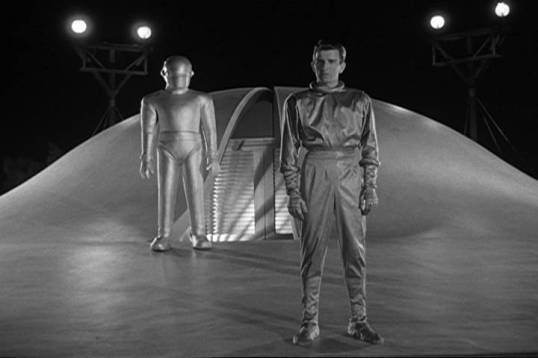
When I purchased the relatively recent remake of “The Day the Earth Stood Still”, it included a nice remastered copy of the 1950 original so my money wasn’t a total waste.
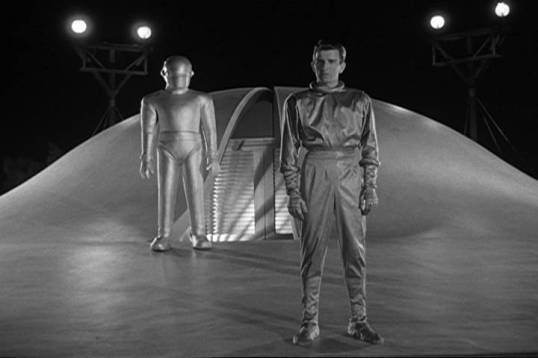
If you’ve never seen it (Ai! What rock have you been living under?) it is based on the timeless story by Harry Bates, “Farewell to the Master,” which is worth a read all by itself.
Long seared having been seared into my mind since the first time I saw it as a child, I’m gratified that this film ranks 7th on Arthur C. Clarke’s top-10 science fiction film list, because even 65 years later – coincidentally my age – it’s just as relevant now as it was then. It’s a tight film, without a second wasted, and made with the intention that it would:
a) be as realistic as the technology allowed, and
b) transmit the message that mankind needs to get rid of its violent nature if it cares to survive.
Having spent a career as a linguist, I some time ago watched the film again with the intent of listening to Klaatu’s language, and transcribing what he said as accurately as possible. There is so little dialog that it can’t really be considered a conlang, but it was interesting to me nonetheless.
“Klaatu barada nikto!” is one of the most famous lines ever uttered in a science-fiction film, but was not the only thing that Klaatu said. The remainder of the dialog is:
Gort! Deglet ovrosco! (Said after Klaatu is shot the first time)
Imray Klaatu naruwak.
Makro [pluvau|pluval], baratu lokdeniso impeklis.
Yavo tari [axo|axel] bugletio barengi degas.
(Klaatu’s instructions – ostensibly to his Federation – for his “demonstration of power”; this linguist’s best transcription. Two words are nearly impossible to pinpoint without a script or screenplay. You can listen to the dialog here.)
Klaatu barada nikto! (Probably something like “Klaatu needs help!”)
Gort, berengo. Probably much like “Mirab, his sails unfurled,” i.e. Gort, let’s blow this bait shack.
I never tire of watching this film – its value to the human condition, and as an early example of outstanding science fiction cinematography, will never diminish.
Here is the text of Klaatu’s speech, for your consideration:
“I am leaving soon, and you will forgive me if I speak bluntly. The universe grows smaller every day, and the threat of aggression by any group, anywhere, can no longer be tolerated. There must be security for all, or no one is secure. Now, this does not mean giving up any freedom, except the freedom to act irresponsibly. Your ancestors knew this when they made laws to govern themselves and hired policemen to enforce them. We, of the other planets, have long accepted this principle. We have an organization for the mutual protection of all planets and for the complete elimination of aggression. The test of any such higher authority is, of course, the police force that supports it. For our policemen, we created a race of robots. Their function is to patrol the planets in spaceships like this one and preserve the peace. In matters of aggression, we have given them absolute power over us. This power cannot be revoked. At the first sign of violence, they act automatically against the aggressor. The penalty for provoking their action is too terrible to risk. The result is, we live in peace, without arms or armies, secure in the knowledge that we are free from aggression and war. Free to pursue more… profitable enterprises. Now, we do not pretend to have achieved perfection, but we do have a system, and it works. I came here to give you these facts. It is no concern of ours how you run your own planet, but if you threaten to extend your violence, this Earth of yours will be reduced to a burned-out cinder. Your choice is simple: join us and live in peace, or pursue your present course and face obliteration. We shall be waiting for your answer. The decision rests with you.”
The Old Wolf has spoken.