As the internet becomes ever more complex, scammers become ever more creative. I hear far too many stories of even computer-savvy people being taken in by fraudsters, and losing substantial sums of money to these jimakplons.¹
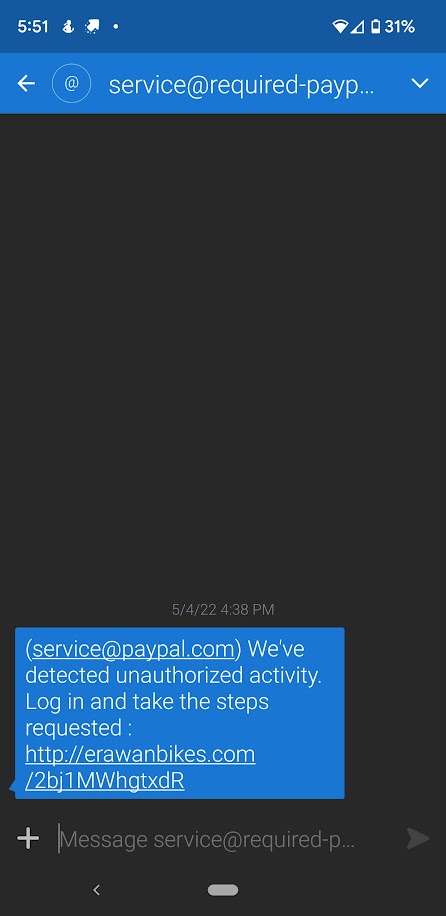
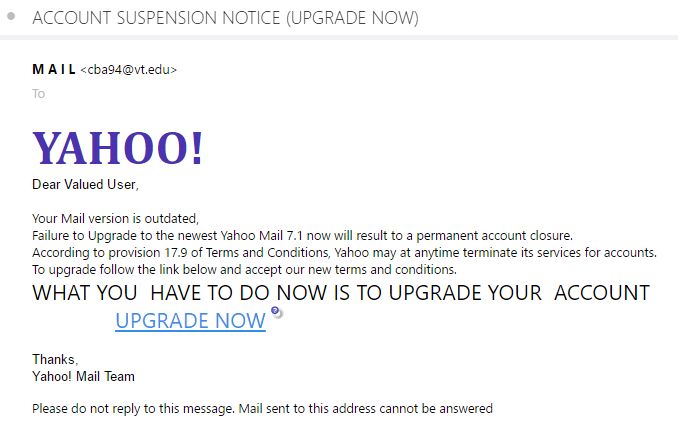
Here’s one that I encountered recently and dove down the rabbit hole to see where it would lead.
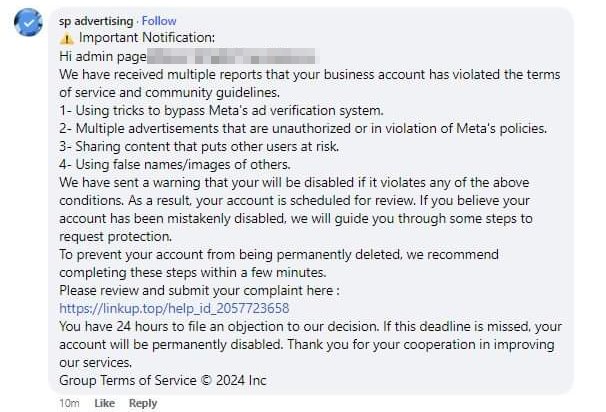
This was a Facebook post that appeared on someone’s company page. It looks pretty realistic, as though it actually could have come from Meta. I was intrigued enough to follow that link (Kids, don’t try this at home).
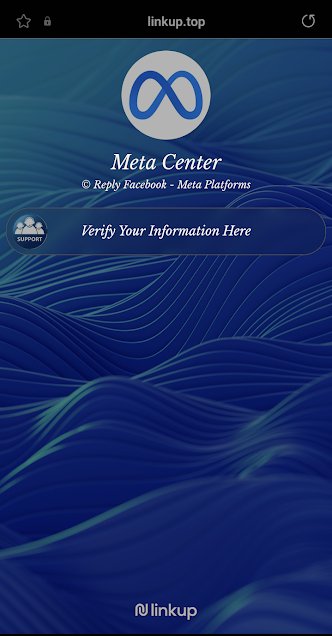
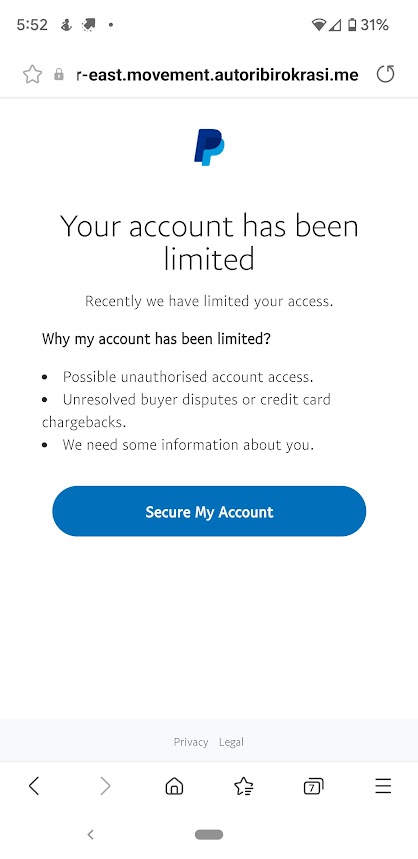
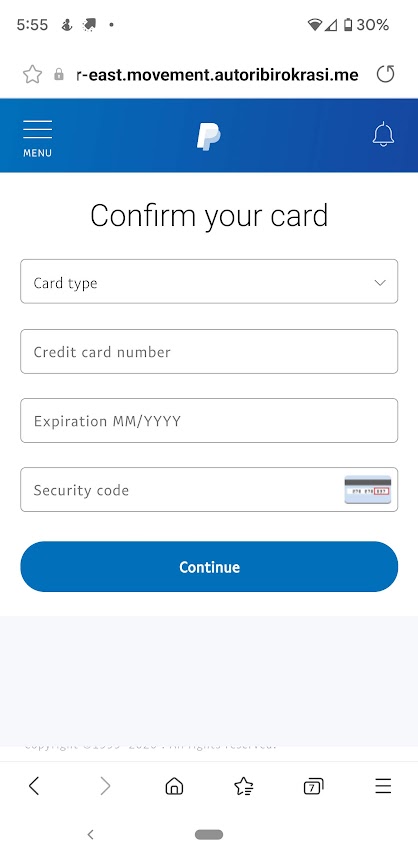
I did this on my mobile device, which is less susceptible to desktop viruses. (Not totally immune, but safer.) This landing page looks OK on the surface, other than that Meta – or any other legitimate company – would not use “linkup . top” as a domain name, seen at the top of the screen.
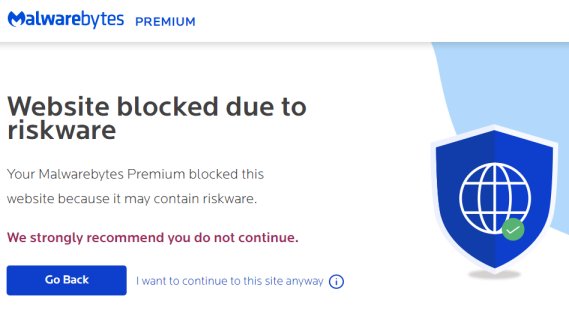
Not sure? This is what I got when I visited that website from my home computer:
Hmm… that’s a pretty good indicator that you don’t want to be anywhere near this website, because you are likely to get bad software (ransomware, trojans, key-loggers, etc) injected onto your computer. But for the sake of public education, here we go:
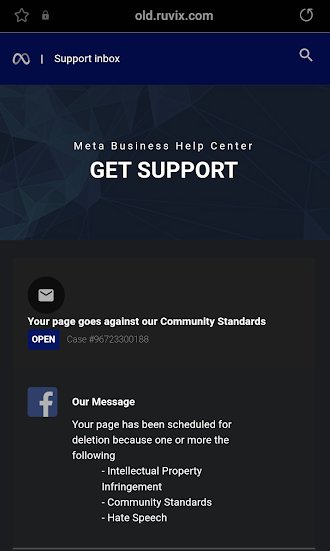
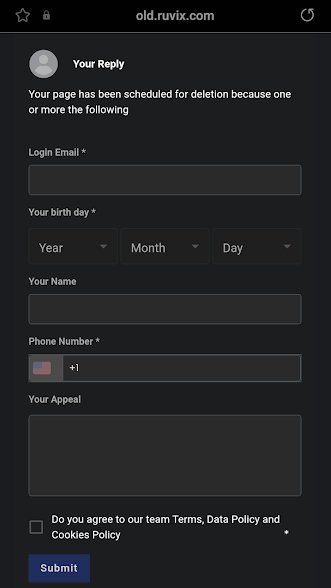
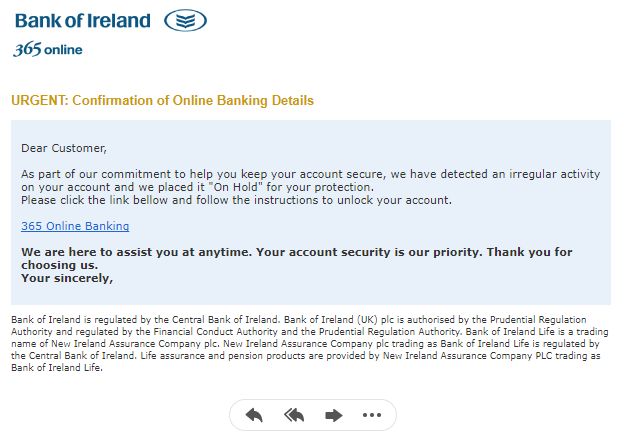
Also claims to be from Meta, but again the URL at the top of the screen is “old . ruvix . com,” which Malwarebytes blocks as a Phishing site.
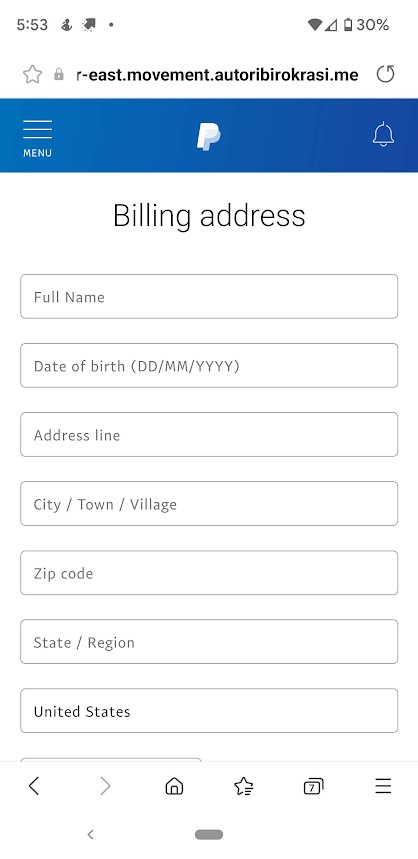
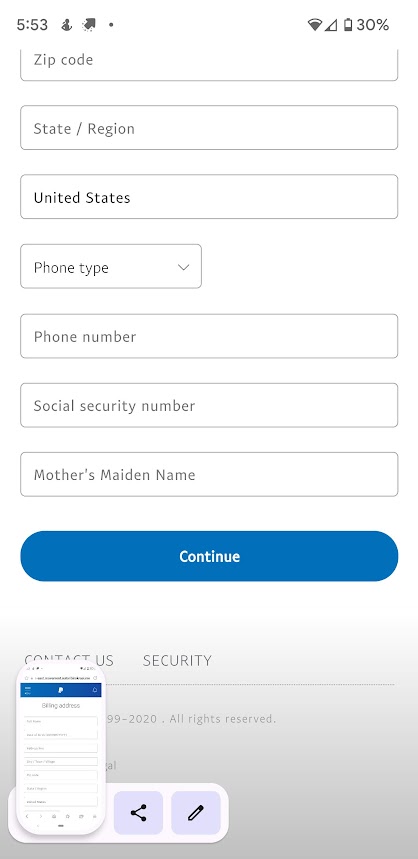
Second screen, where they scammers begin to gather your information, starting with that highly-coveted birthdate, and a phone number.
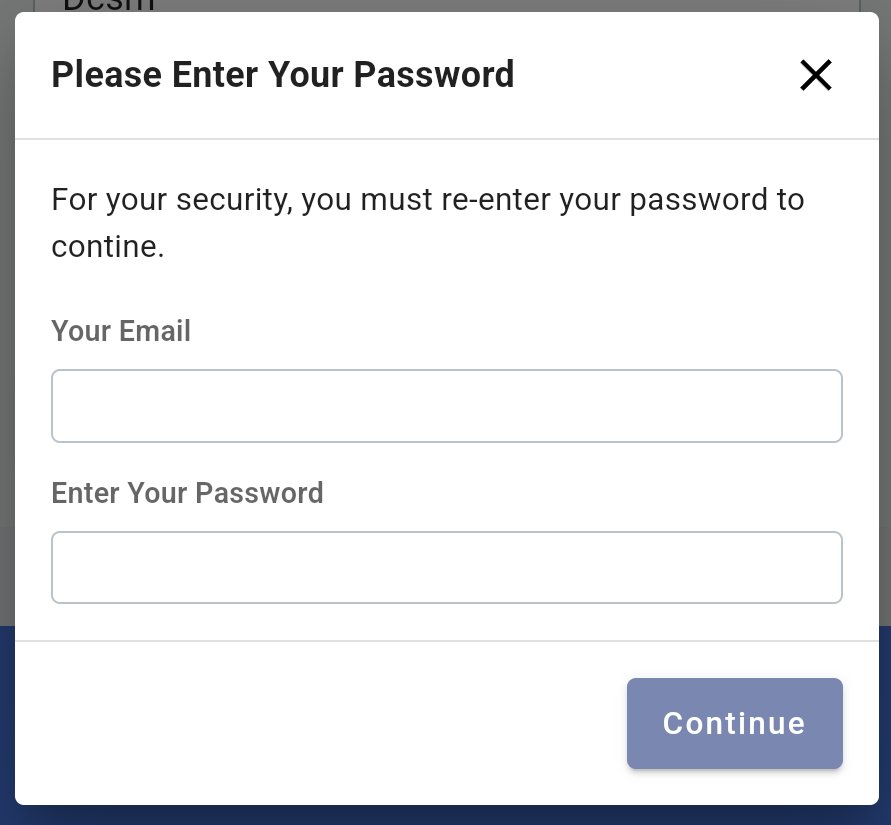
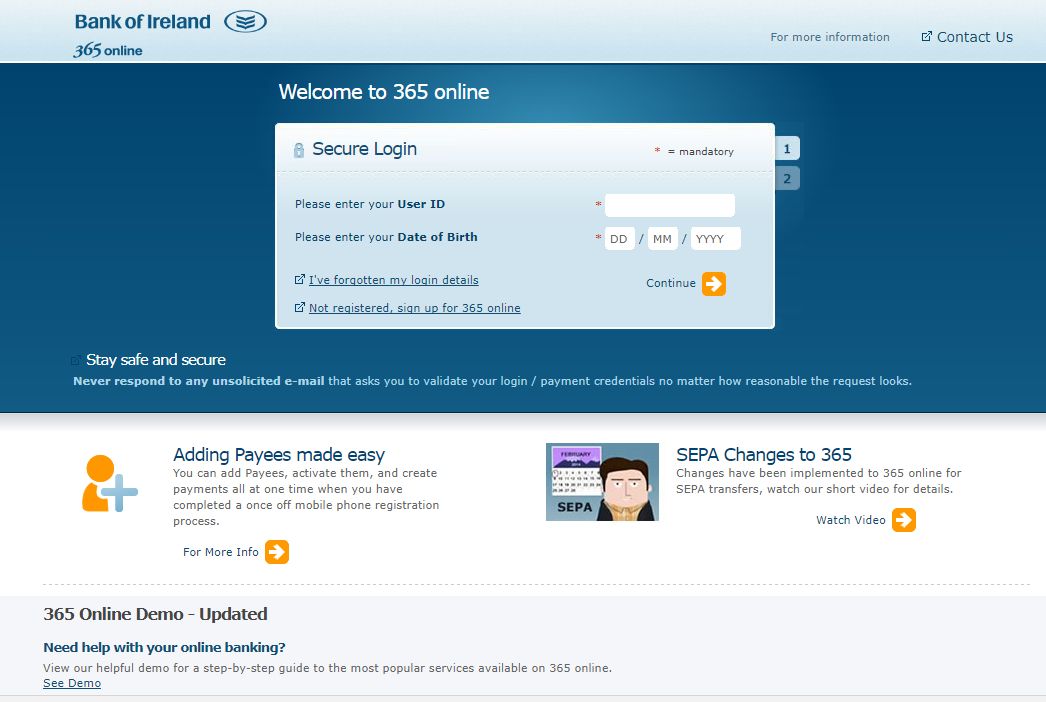
No matter what the victim enters, they get this screen, ostensibly to obtain their Facebook UserID and Password. No matter what is typed, an error message is given saying that the password was incorrect, and asks for the same information again. It does not matter what is entered – the second try will always succeed.
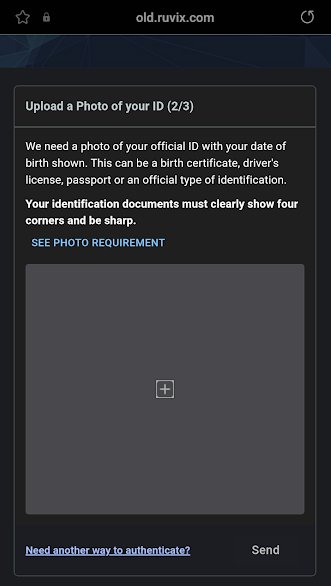
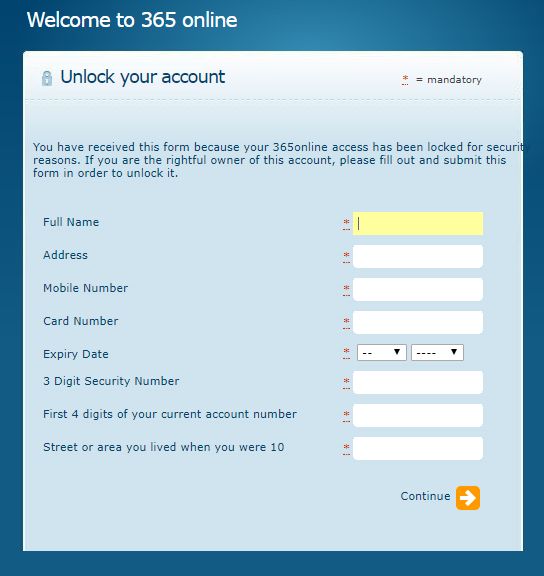
This is a fairly new one on me. Unless I’m dealing with a Nigerian scammer, I’ve never had a phishing website ask for a picture of my ID. OK, I’m game:
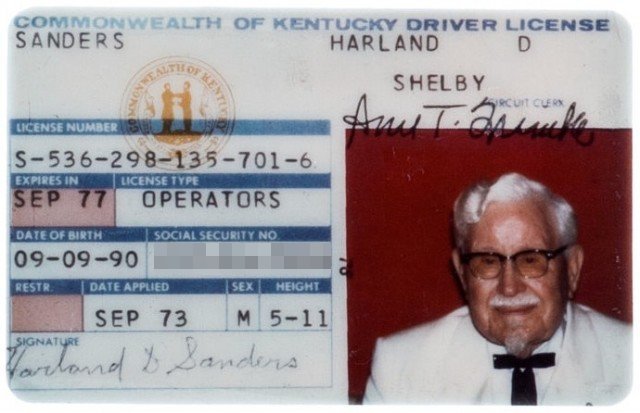
I’m sure the scammers had fun with this one. (I obscured the SS Number just in case it was real – scammers can use the Social Security Numbers of dead people just as easily as living ones for their nefarious purposes.)
At this point, the page actually returns you to a real Meta page, and the scammers trot off happily into the sunset to use the victim’s information for whatever evil they have planned.
Be oh, so careful out there. Practice safe computing, and protect your vulnerable loved ones.
The Old Wolf has spoken.
Footnotes
¹ To call someone a “jimakplon” in Benin is a terrible insult to one’s parents. It was defined thusly over at “Friends of Bonou”:
Question: Actually this reminds me: it is also true about an insult that Europeans would find laughably mild and that is really serious in Benin: it is when you are accused of being impolite: You loose face totally if you are insulted like that, apparently: Why?
Answer: Ah. It is because “Impolite” is a translation of a Fon word, “jimakplon.” = “Ji” means “born,” “ma” means “not,” and “kplon” means “teach.” So what “jimakplon” really means is “born but not taught.” You were born into this world but didn’t receive any social education. So this is serious because it is an insult against the parents of the person you’re talking to: “Impolite” is a slur on the parents of the person you’re insulting, who didn’t give them a social education, and this is a BIG face loss!
It’s a term I find entirely appropriate to describe these ignorant scammers.