Thieves want your information and your money. They’ll take it any way they can get it. Eastern Europe is a hotbed of cyber-crime but, sensing the opportunity for profit, other nations are getting into the act, and the same old techniques resurface.
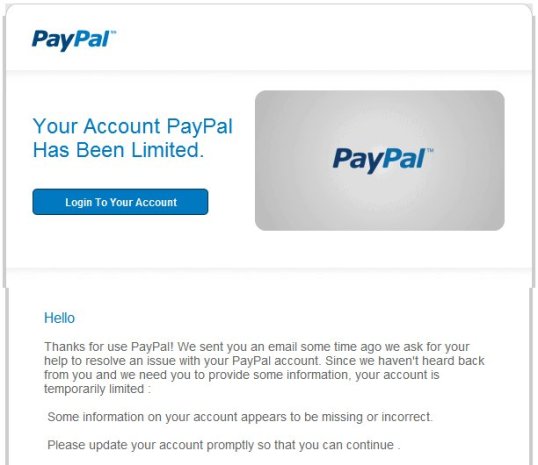
Here’s a typical phishing scam email which landed in my inbox today. Protect yourself, be aware, exercise safe computing, and warn your loved ones. This stands to be repeated often and loudly.
|
From: service@chase.com<gpwtnf@admin.net>
To: admin@chase.com
Subject: NOTICE ID : DXEUWSPLNT |
Dear Chase Bank Customer
It has come to our attention that your Chase Bank account information needs to be
updated as part of our continuing commitment to protect your account and to
reduce the instance of fraud on our website. If you could please take 5-10 minutes
out of your online experience and update your personal records you will not run into
any future problems with the online service.
To update your Chase records click on the following link:
Thank you for your patience in this matter.
Sincerely,
Ammy Smith,
Chase Bank Security Departament.
Please do not reply to this e-mail as this is only a notification. Mail sent to this address cannot be answered.
Copyright 2012, CHASE BANK SERVICE, INC. All Rights Reserved.
NICHMOKENLWJJFLDBVSKYXRCHQRWEFILLLKYSO
Right. First off, look at anything that’s green in the email above. These are red flags.
1) Garbage text. Any email that contains strings of junk or random English words strung together is trying to thwart Bayesian spam filtering. It’s a complex algorithgm that is employed by service providers and email clients to try to keep Spam from ever getting to you.
2) Mis-spellings. While human error is possible, most legitimate companies (especially large financial institutions like Chase) are pretty careful about the quality of messages they send out. Bad English, strange punctuation, odd collocations and mis-spellings are all red flags for fraudulent activity (which includes most spam, by the way).
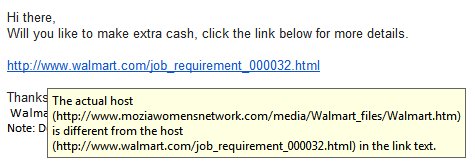
3) Garbage or misdirected links. Just because a web address has the word “Chase” in it doesn’t mean that it’s from Chase. URL’s that contain alphabet soup are to be regarded very suspiciously. Never click on links from an email, especially if the word “money” or “finances” enters into the equation. If you have an account with Wells Fargo, for example, go directly to wellsfargo.com with your browser.
As it turns out, the link above redirects you to this URL:
http://[Link Removed].endoftheinternet.org/chs/chk/index1.php
?source=chase&customer=CrazvSTcCtTvoOIhYiLNI1bplxauXFAqWAQijzkM
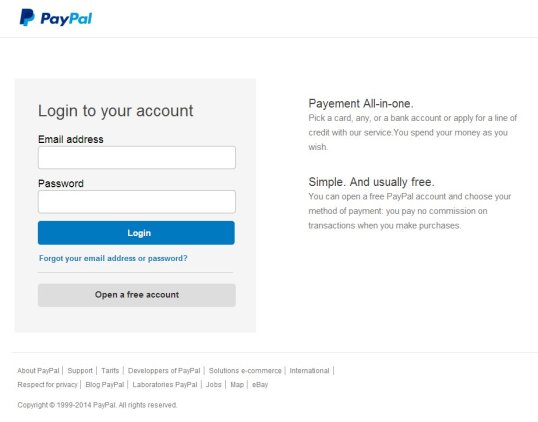
(I obfuscated the link to make sure nobody actually clicks on this and goes there.) If you did, what you would see is this:

It looks very, very authentic – except for that garbage URL. In fact, the scammers copied the actual http://chase.com website exactly. If you enter your UserID and password, bingo! You’ve just given Russian cyber-criminals access to all your accounts.
Again: Never click on links inside an email. Always type addresses directly into your browser window to make sure you’re going to the real company’s website.
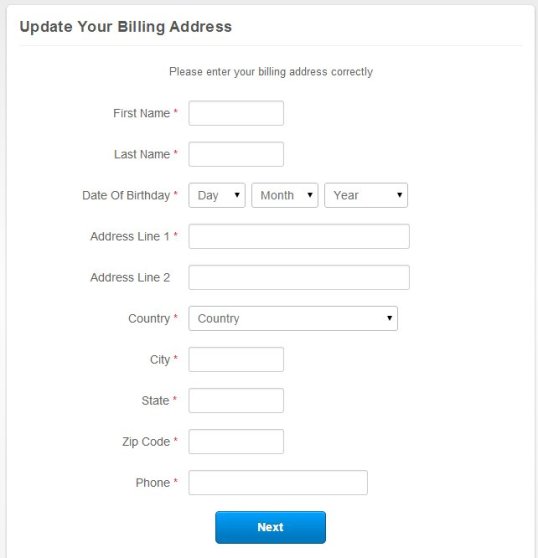
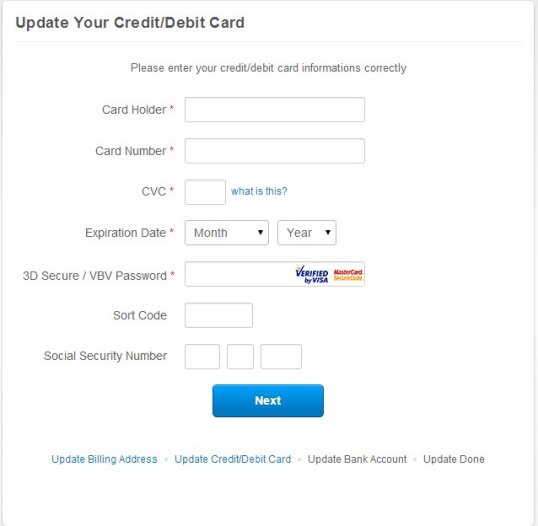
These particular drones aren’t through with you yet, though. If you enter your information (I put in some really insulting stuff which I can’t repeat here), you’ll be taken to this URL:
http://%5BLink Removed].chaseonline.chase.com.crazvstccttvooihyilni1bplxauxfaqwaqijzkm.
csqifywdn.endoftheinternet.org/chs/chk/email.php
which gives you this page:

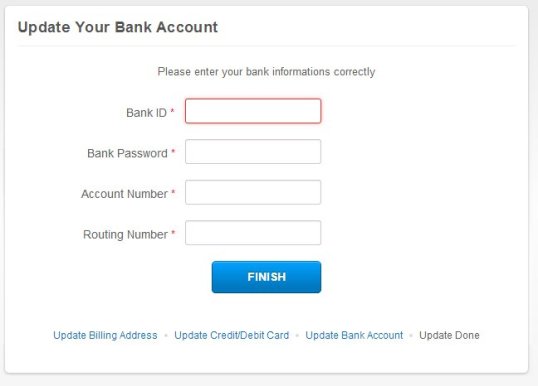
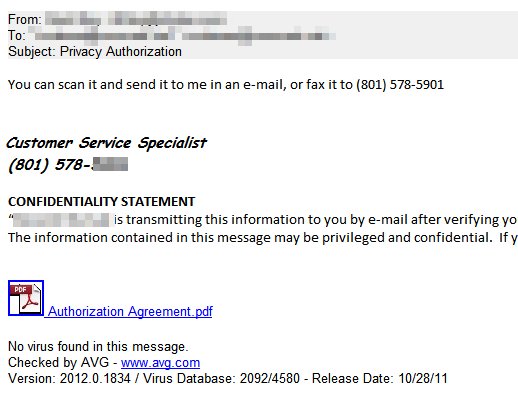
So these scumsuckers not only want your financial data, they want access to your email account as well, so they can scam all your friends and send messages from your account.
If you’re aware of these antics, they seem pretty transparent. Unfortunately, a huge percentage of our population is working with computers and the Internet at a “cookbook” level, without any more than a superficial understanding of what they are doing. There’s no judgement around that – it’s great that they’re learning new skills. But if you have loved ones, especially elderly family members who fall into that category, please make sure they are watched over and educated.
Practice Safe Computing
1) Be afraid of any email that includes the words
- “Verify your account.”
- “Update your account.”
- “During regular account maintenance…”
- “Failure to update your records will result in account suspension.”
or similar things. Legitimate organizations will never ask for your ID or sensitive information by email or telephone
2) Do not click on links inside an email. Always go directly to your financial institution’s website from your browser.
3)Never send sensitive information to anyone in an email. Even if it’s legitimate, emails can be intercepted and read by the bad guys.
Be careful out there, it’s a jungle.
The Old Wolf has spoken.








 , clicking
, clicking 

